The Latest
-
New RFP Template for AI Usage Control and AI Governance
-
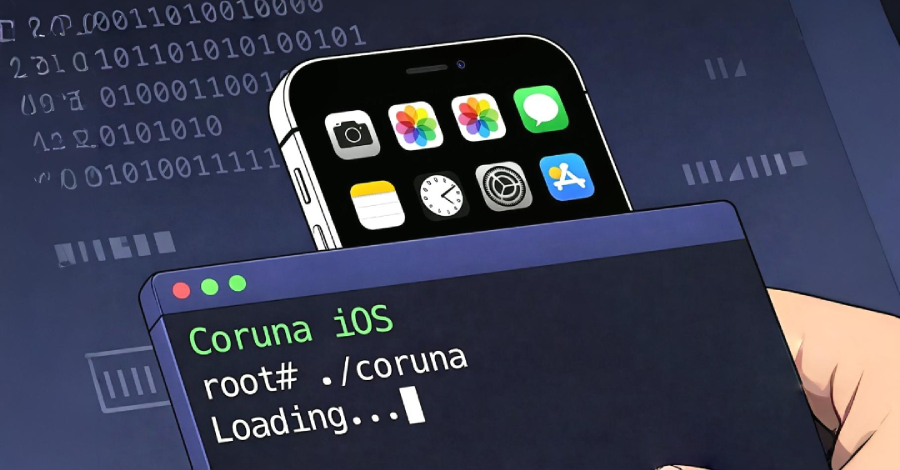
Coruna iOS Exploit Kit Uses 23 Exploits Across Five Chains Targeting iOS 13–17.2.1
-
149 Hacktivist DDoS Attacks Hit 110 Organizations in 16 Countries After Middle East Conflict
-
Speakeasies to Shadow AI: Banning AI Browsers Will Fail