The Latest
-
Starkiller Phishing Suite Uses AitM Reverse Proxy to Bypass Multi-Factor Authentication
-
AI Agents: The Next Wave Identity Dark Matter – Powerful, Invisible, and Unmanaged
-
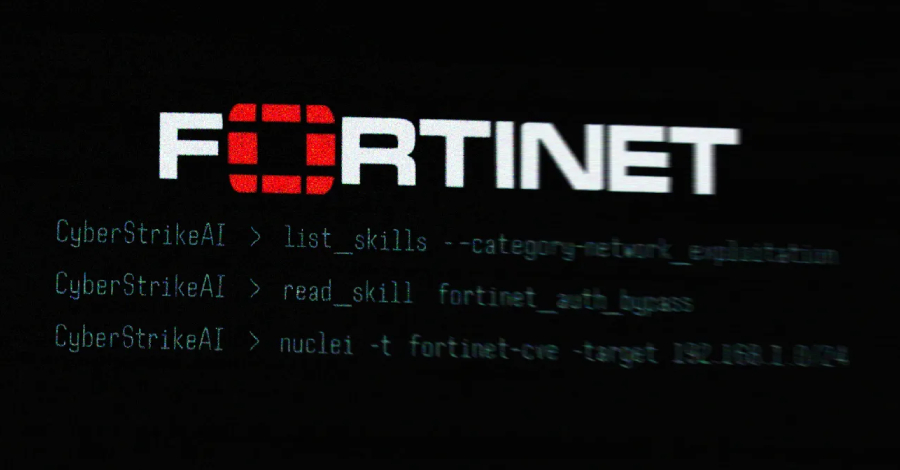
Open-Source CyberStrikeAI Deployed in AI-Driven FortiGate Attacks Across 55 Countries
-
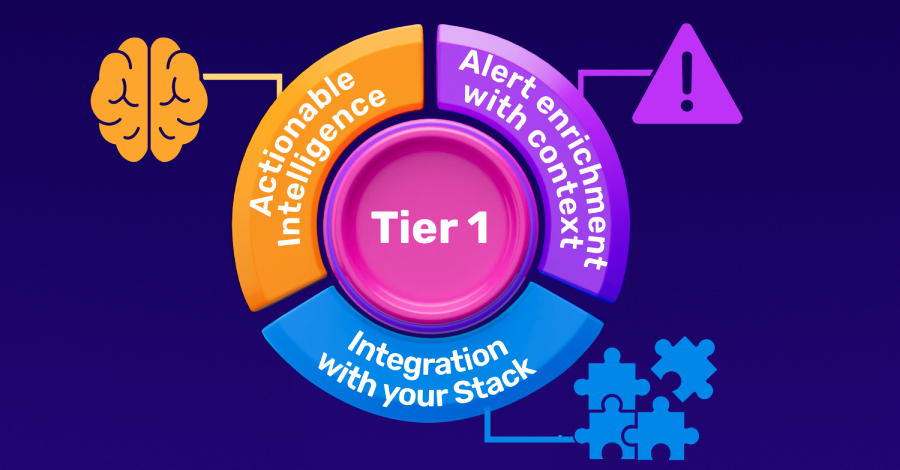
Building a High-Impact Tier 1: The 3 Steps CISOs Must Follow