The Latest
-
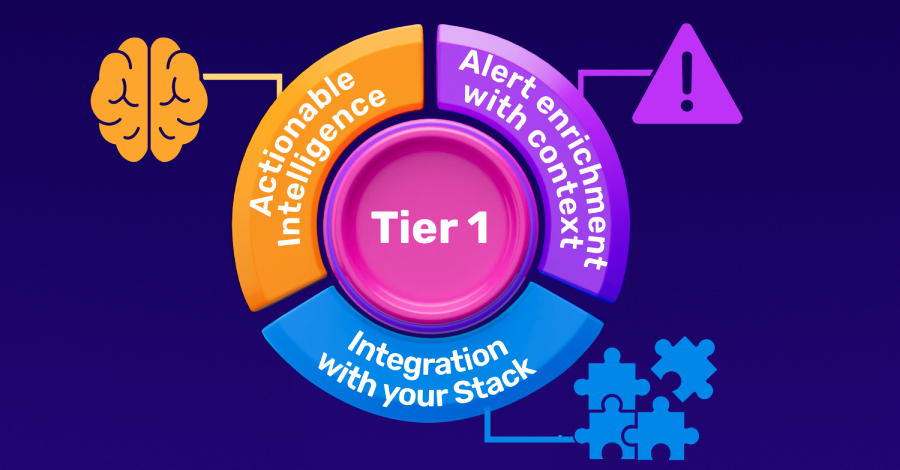
Building a High-Impact Tier 1: The 3 Steps CISOs Must Follow
-
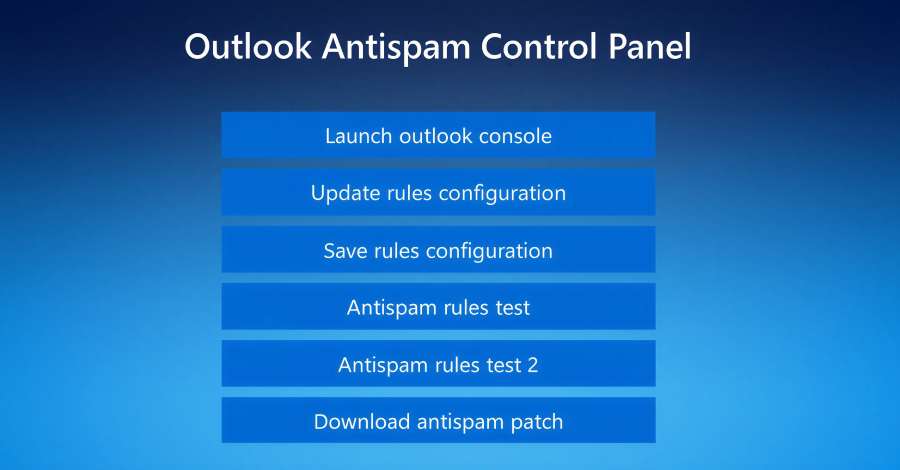
Fake Tech Support Spam Deploys Customized Havoc C2 Across Organizations
-
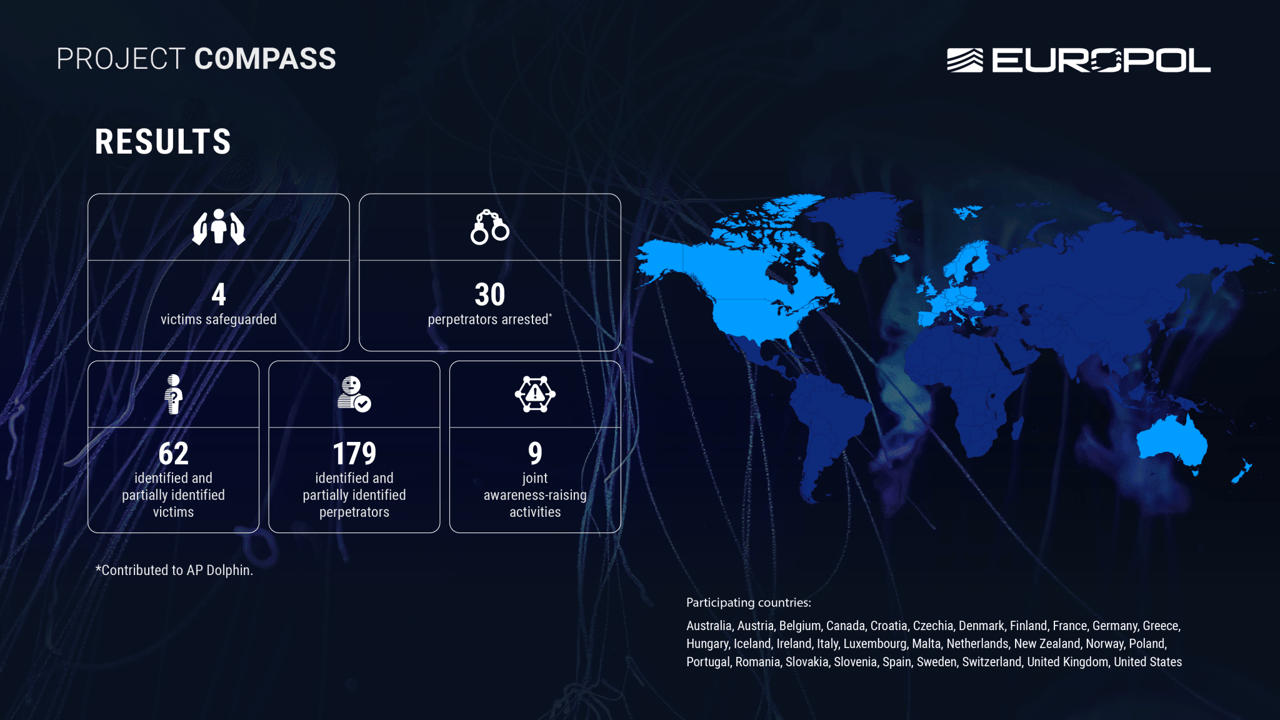
30 Alleged Members of 'The Com' Arrested in Project Compass
-
The Tug-of-War Over Firewall Backlogs in the AI-Driven Development Era