With the FIFA World Cup coming to the United States, Canada, and Mexico this year, cybersecurity experts are warning that the risks are rising from rapidly evolving threats such as drones and wireless surveillance.
Wireless communications have grown in importance and criticality, with connections to security systems, operational technology (OT), and application connectivity all expanding dramatically over the past decade. One major application for wireless communications are drones, which have been used increasingly in conflict zones and pose potentially greater dangers for civilian populations.
The concern is that threat actors will translate what they have learned to civilian settings, says Cordell Bennigson, CEO for the US market at R2 Wireless, a company focused on real-time radio-frequency monitoring.
“There’s definitely a risk of disruption to operational technology (OT), such as stadium systems, traffic management, or public safety communications, particularly when those systems have wireless components,” he says. “The key issue is not having visibility, because cities can’t defend what they can’t see.”
In 2026, the FIFA World Cup is expanding to 16 stadiums in cities peppered throughout Canada, Mexico, and the US. The tournament will be bigger in every way from past events, with 48 teams playing 104 games, and will require a massive increase in reliance on technology and automation.
At the same time, physical cyber threats have matured rapidly since Russia invaded Ukraine four years ago. First-person-view (FPV) drones regularly surveil the battlefield in Ukraine, making tank and troop movements a far more deadly gamble and drone the primary cause of casualties, with current estimates attributing 80% of deaths and injuries to drones, compared to less than 10% at the start of the war, according to Reuters.
A Complex Wireless Environment
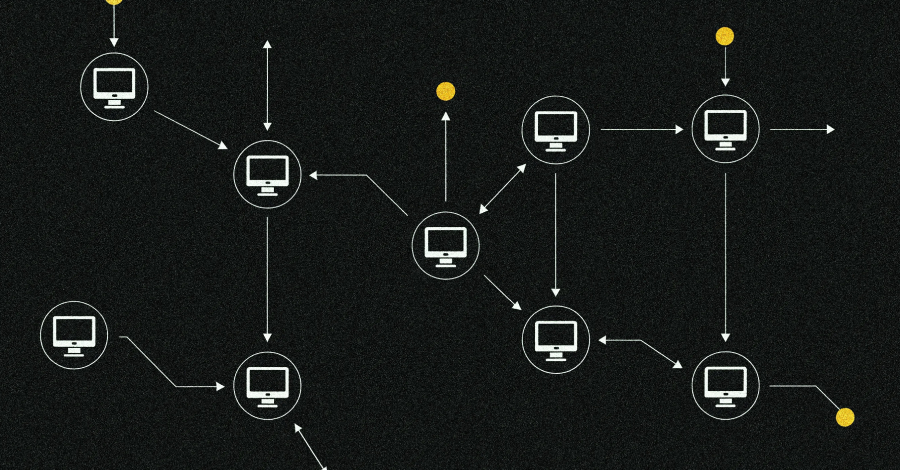
During major events like the FIFA World Cup, host cities will face “one of the most complex radio-frequency (RF) environments a city will ever experience,” R2 Wireless’s Bennigson says. “You’re looking at hundreds of thousands of people, thousands of devices, broadcast infrastructure, public safety communications, temporary networks, and increasingly autonomous systems, which all operate simultaneously in a compressed geographic area.”
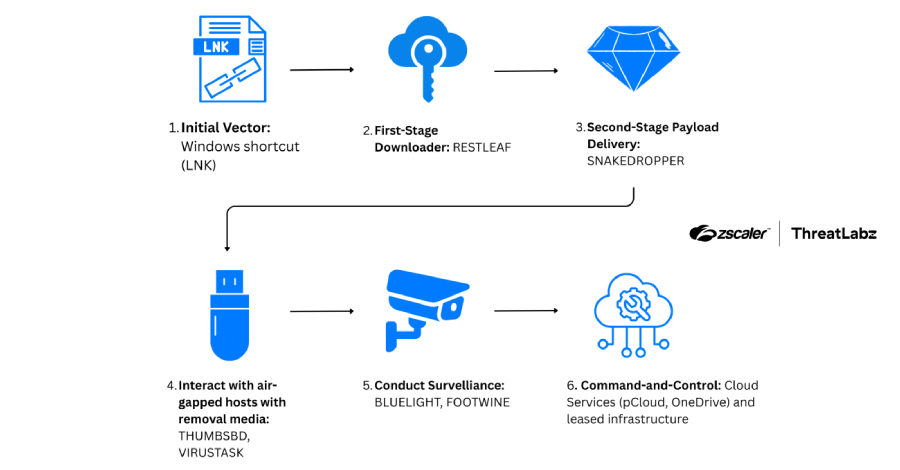
Active wireless threats include attempts to hijack or jam the command-and-control (C2) signals used by event managers to operate and secure the venues, while the wireless networks can also be used to compromise event systems. Modern wireless networks, such as 5G cellular, have suffered increasing attacks, with wireless equipment provider Nokia concluding, “Breaches are the rule, not the exception.”
Finally, drone operations rely almost exclusively on wireless signals and can carry sensors to conduct wireless surveillance and harvest communications. While the drones are vulnerable to jamming, many operate over commercial cellular networks and others use onboard AI to make wireless connectivity unnecessary.
In many cases, local civilian law enforcement lack the authority to fight back against such threats, says Krishna Vishnubhotla, vice president of product strategy at Zimperium, a mobile security solutions firm.
“Most local law enforcement can’t even use basic counter-drone tools,” he says. “The 2026 World Cup … is a prime target, [and] drones, wireless surveillance, and cascading infrastructure failures are all credible threats at an event of that scale.”
Passive Cyber Aggression
Such active threats are not the only concerns. Using wireless to monitor and map the location of a device, harvest metadata, and conduct airborne or ground-based surveillance are all concerns at large events, says R2 Wireless’s Bennigson. Because large events rely heavily on temporary communications infrastructure and fast deployment of broadcast technology, public safety radios, and Internet of Things (IoT) deployments, attackers have a plethora of targets, he says.
“The RF spectrum becomes both the battlefield and the blind spot,” he says. “In a high-density RF environment, we can expect malicious actors to hide within legitimate traffic. The noise becomes their cover.”
Overall, event managers need to have the wireless spectrum locked down in the region of any major events like the FIFA World Cup, says Vishnubhotla.
“Effective defense requires layering RF, radar, acoustic, and optical detection together, since adversaries actively exploit any single system’s blind spots,” he says, adding that both the EU and US are adopting AI-driven spectrum monitoring and putting controls in place to limit cellular control of drones and other anti-drone technology.
Vishnubhotla adds that training personnel to operate in hostile wireless environments is critical to minimizing risks at major events in the future.
Source: www.darkreading.com…