Cybersecurity researchers have called attention to a “massive campaign” that has systematically targeted cloud native environments to set up malicious infrastructure for follow-on exploitation.
The activity, observed around December 25, 2025, and described as “worm-driven,” leveraged exposed Docker APIs, Kubernetes clusters, Ray dashboards, and Redis servers, along with the recently disclosed React2Shell (CVE-2025-55182, CVSS score: 10.0) vulnerability. The campaign has been attributed to a threat cluster known as TeamPCP (aka DeadCatx3, PCPcat, PersyPCP, and ShellForce).
TeamPCP is known to be active since at least November 2025, with the first instance of Telegram activity dating back to July 30, 2025. The TeamPCP Telegram channel currently has over 700 members, where the group publishes stolen data from diverse victims across Canada, Serbia, South Korea, the U.A.E., and the U.S. Details of the threat actor were first documented by Beelzebub in December 2025 under the name Operation PCPcat.
“The operation’s goals were to build a distributed proxy and scanning infrastructure at scale, then compromise servers to exfiltrate data, deploy ransomware, conduct extortion, and mine cryptocurrency,” Flare security researcher Assaf Morag said in a report published last week.
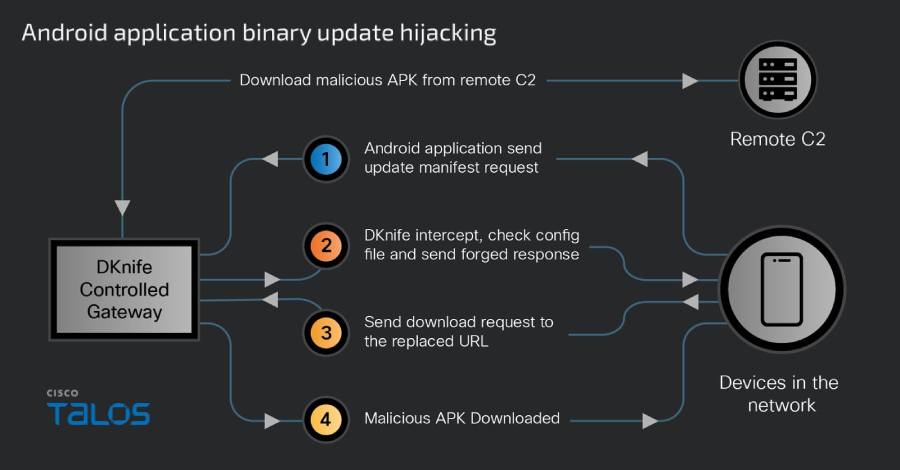
TeamPCP is said to function as a cloud-native cybercrime platform, leveraging misconfigured Docker APIs, Kubernetes APIs, Ray dashboards, Redis servers, and vulnerable React/Next.js applications as main infection pathways to breach modern cloud infrastructure to facilitate data theft and extortion.
In addition, the compromised infrastructure is misused for a wide range of other purposes, ranging from cryptocurrency mining and data hosting to proxy and command-and-control (C2) relays.
Rather than employing any novel tradecraft, TeamPCP leans on tried-and-tested attack techniques, such as existing tools, known vulnerabilities, and prevalent misconfigurations, to build an exploitation platform that automates and industrializes the whole process. This, in turn, transforms the exposed infrastructure into a “self-propagating criminal ecosystem,” Flare noted.
Successful exploitation paves the way for the deployment of next-stage payloads from external servers, including shell- and Python-based scripts that seek out new targets for further expansion. One of the core components is “proxy.sh,” which installs proxy, peer-to-peer (P2P), and tunneling utilities, and delivers various scanners to continuously search the internet for vulnerable and misconfigured servers.
“Notably, proxy.sh performs environment fingerprinting at execution time,” Morag said. “Early in its runtime, it checks whether it is running inside a Kubernetes cluster.”
“If a Kubernetes environment is detected, the script branches into a separate execution path and drops a cluster-specific secondary payload, indicating that TeamPCP maintains distinct tooling and tradecraft for cloud-native targets rather than relying on generic Linux malware alone.”
A brief description of the other payloads is as follows –
- scanner.py, which is designed to find misconfigured Docker APIs and Ray dashboards by downloading Classless Inter-Domain Routing (CIDR) lists from a GitHub account named “DeadCatx3,” while also featuring options to run a cryptocurrency miner (“mine.sh”).
- kube.py, which includes Kubernetes-specific functionality to conduct cluster credential harvesting and API-based discovery of resources such as pods and namespaces, followed by dropping “proxy.sh” into accessible pods for broader propagation and setting up a persistent backdoor by deploying a privileged pod on every node that mounts the host.
- react.py, which is designed to exploit the React flaw (CVE-2025-29927) to achieve remote command execution at scale.
- pcpcat.py, which is designed to discover exposed Docker APIs and Ray dashboards across large IP address ranges and automatically deploy a malicious container or job that executes a Base64-encoded payload.
Flare said the C2 server node located at 67.217.57[.]240 has also been linked to the operation of Sliver, an open-source C2 framework that’s known to be abused by threat actors for post-exploitation purposes.
Data from the cybersecurity company shows that the threat actors mainly single out Amazon Web Services (AWS) and Microsoft Azure environments. The attacks are assessed to be opportunistic in nature, primarily targeting infrastructure that supports its goals rather than going after specific industries. The result is that organizations that run such infrastructure become “collateral victims” in the process.
“The PCPcat campaign demonstrates a full lifecycle of scanning, exploitation, persistence, tunneling, data theft, and monetization built specifically for modern cloud infrastructure,” Morag said. “What makes TeamPCP dangerous is not technical novelty, but their operational integration and scale. Deeper analysis shows that most of their exploits and malware are based on well-known vulnerabilities and lightly modified open-source tools.”
“At the same time, TeamPCP blends infrastructure exploitation with data theft and extortion. Leaked CV databases, identity records, and corporate data are published through ShellForce to fuel ransomware, fraud, and cybercrime reputation building. This hybrid model allows the group to monetize both compute and information, giving it multiple revenue streams and resilience against takedowns.”
Source: thehackernews.com…